San José, Costa Rica – May 11, 2022 – In a move that underscores the escalating global ransomware threat, Costa Rican President Rodrigo Chaves declares a national emergency as the infamous Conti ransomware syndicate paralyzes multiple government ministries. The attack, which surfaces publicly on May 2, now disrupts critical services nationwide, forcing officials into a desperate race to restore functionality while fending off hackers' extortion demands.
The Attack Unfolds
The cyber intrusion targets the Ministry of Finance's Hacienda tax authority first. Hackers infiltrate the network, encrypt vital data, and exfiltrate sensitive information including taxpayer records and internal documents. Conti, a Russian-speaking ransomware-as-a-service (RaaS) operation known for high-profile hits like Ireland's Health Service Executive in 2021, quickly claims responsibility on its dark web leak site.
By May 5, the malware spreads to the ministries of Labor, Science and Technology, and Environment. Government portals go dark, payroll processing halts, and public services grind to a standstill. Employees report locked computers displaying ransom notes demanding cryptocurrency payments – reportedly $5 million initially, though exact figures remain unconfirmed by authorities.
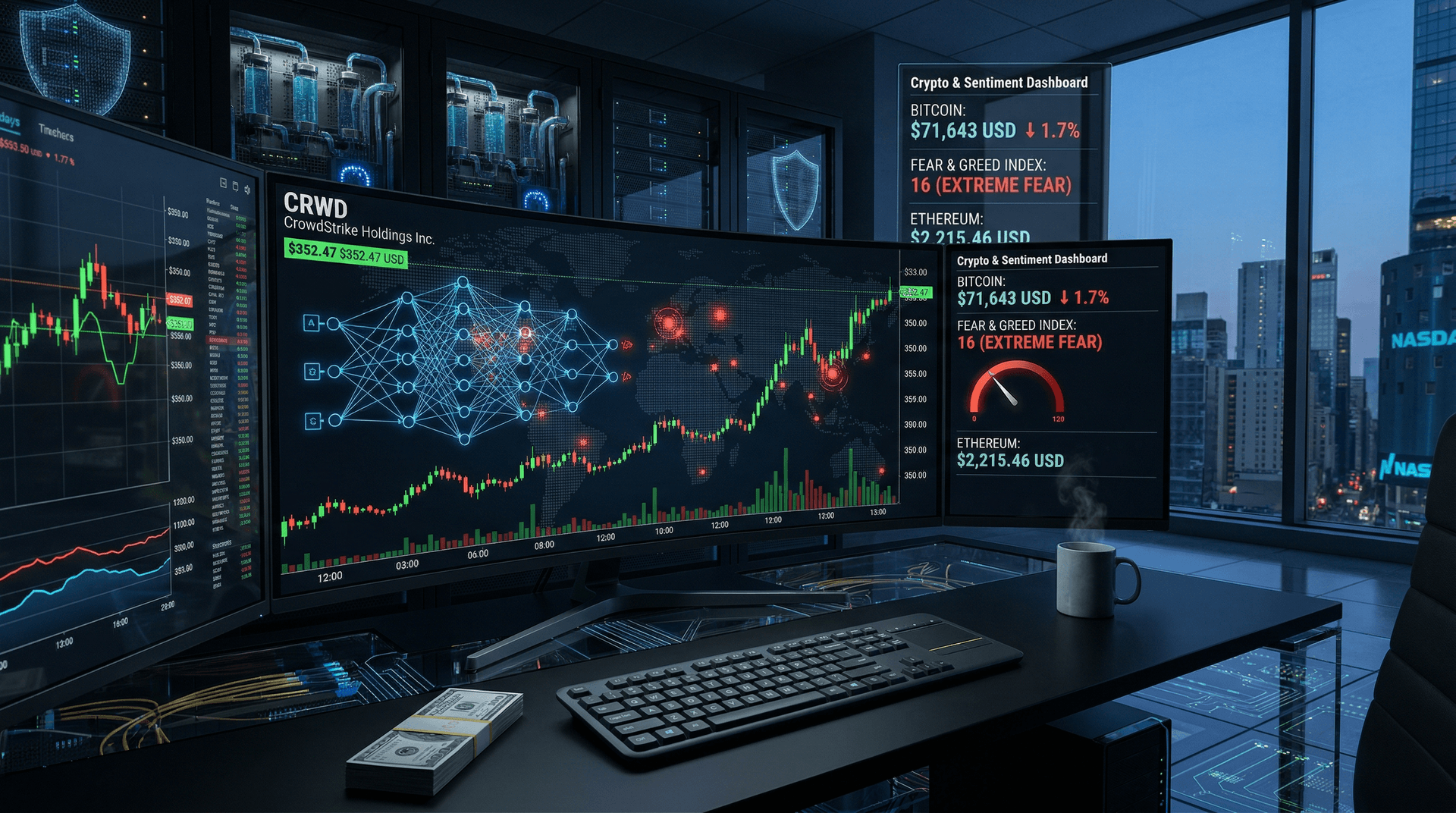
President Chaves, sworn in just days earlier on May 8, addresses the nation: "This is an attack on our sovereignty. We will not negotiate with criminals." His administration activates emergency protocols, shifting to manual operations where possible and enlisting international aid from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and private firms like CrowdStrike.
Conti's Shadowy Profile and Motives
Conti emerges as one of the most prolific ransomware groups since 2020, amassing over $180 million in ransoms by some estimates. Operating via a RaaS model, affiliates pay Conti a cut of extorted funds in exchange for malware tools and negotiation support. The group targets sectors from healthcare to critical infrastructure, with attacks peaking amid geopolitical tensions.
Ironically, Conti pledges support for Russia's invasion of Ukraine in late February 2022, leaking internal chats when challenged. Yet, it strikes Costa Rica, a neutral nation with no apparent geopolitical beef. Cybersecurity experts speculate financial motives drive the hit, as Costa Rica's digital transformation leaves legacy systems vulnerable.
"Conti's opportunism knows no borders," says Allan Liska, ransomware analyst at Recorded Future. "They exploit weak perimeter defenses – unpatched VPNs, exposed RDP ports – common in government IT. Costa Rica's rapid digitization without matching security investments makes it a prime target."
Immediate Impacts on Daily Life
Costa Ricans feel the ripple effects acutely. Tax filings freeze, delaying refunds and business operations. Labor ministry services, including social security payments, falter, stranding thousands. Environmental monitoring tools offline hamper disaster response in a country prone to hurricanes and volcanoes.
Private sector jitters mount too. Banks report phishing spikes mimicking government alerts, while tourism – Costa Rica's economic lifeline – braces for disruptions in permit processing. "We're in damage control mode," admits Finance Minister Elian Villegas. "Prioritizing essential services like health and security."
Recovery proves arduous. Experts decrypt samples revealing sophisticated encryption, likely using Windows Group Policy for lateral movement. Indicators of compromise (IOCs) circulate via CISA alerts: Conti employs Cobalt Strike beacons and custom loaders evading endpoint detection.
Government Response and International Solidarity
Chaves' emergency decree mobilizes the National Emergency Commission (CNE) and allocates funds for cybersecurity bolstering. The government refuses ransom payment, aligning with U.S. and EU no-pay policies. Instead, it pursues attribution through joint task forces.
U.S. Ambassador Cynthia Telles pledges support: "America stands with Costa Rica against cyber aggression." Microsoft and Google offer cloud forensics pro bono, while INTERPOL coordinates with Costa Rican Judicial Investigation Organism (OIJ).
Locally, the government's Computer Security Incident Response Team (CSIRT-CR) leads triage. They isolate infected systems, patch vulnerabilities, and hunt for persistence mechanisms. "We're rebuilding from backups where available," a CSIRT spokesperson states. "But data integrity checks take time."
Broader Lessons for Global Cybersecurity
This incident spotlights ransomware's evolution. Conti adapts post-Colonial Pipeline (2021), emphasizing data theft over mere encryption. Victims face double extortion: pay or face leaks. Costa Rica's data – 6 terabytes per Conti – includes personal identifiers ripe for identity fraud.
"Governments worldwide must prioritize zero-trust architectures," urges Krebs on Security founder Brian Krebs. "Legacy systems persist due to budget constraints. Costa Rica invests $20 million annually in cyber defenses – insufficient against nation-state-caliber tools Conti wields."
Statistics paint a grim picture. Chainalysis reports ransomware payments hit $1 billion in 2021, with 2022 trending higher. Costa Rica ranks mid-tier in global cyber resilience indices, but Latin America sees 30% attack surge per Check Point Research.
Recommendations emerge: Multi-factor authentication (MFA) enforcement, regular backups offline, and employee training. The EU's NIS2 Directive and U.S. Executive Order 14028 push similar reforms, potentially inspiring Costa Rica's overhaul.
Path Forward Amid Uncertainty
As May 11 dawns, partial restorations occur in Hacienda, but full recovery stretches weeks. Conti ups pressure, leaking samples online – passports, financials – to coerce payment. Officials monitor for destructive wipers, a Conti tactic in Ukraine.
President Chaves vows legislative action: "New cyber laws, dedicated funding, international pacts." Public support swells, with protests decrying digital fragility.
For the world, Costa Rica's plight serves as canary in the coal mine. Ransomware transcends borders, demanding collective defense. As Conti evolves, so must defenders – or face systemic collapse.
CSN News will update as events unfold.
Word count: 942