By [Your Name], Senior Tech Journalist | July 23, 2024
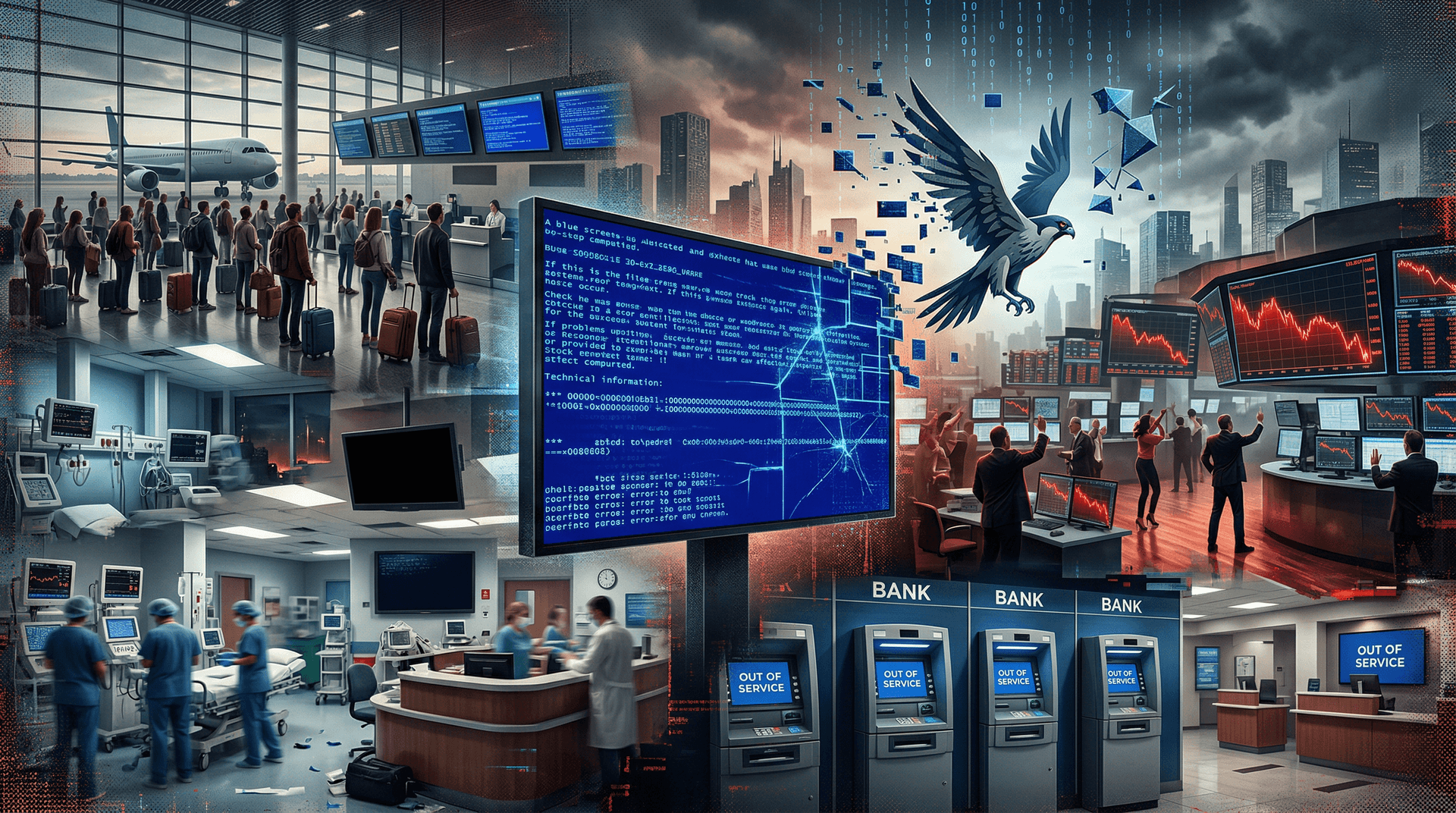
In one of the most significant IT disruptions in recent history, a faulty update deployed by cybersecurity firm CrowdStrike on July 19 has plunged millions of Windows computers into chaos. The incident, which began early Friday morning, continues to ripple through global industries as of today, July 23, with airlines, hospitals, banks, and retailers scrambling to restore operations.
The Trigger: A Content Update Gone Wrong
CrowdStrike, a leading provider of endpoint detection and response (EDR) software, pushed a defective content configuration update to its Falcon Sensor platform around 4:00 UTC on July 19. This update targeted Windows hosts and contained a logic error in a channel file—a component used by the sensor to detect threats.
When the corrupted file loaded into the Windows kernel, it caused systems to enter a boot loop, displaying the infamous Blue Screen of Death (BSOD) with error code 'PAGE_FAULT_IN_NONPAGED_AREA'. Unlike typical malware-induced crashes, this was self-inflicted: a legitimate update from a trusted vendor.
CrowdStrike quickly identified the issue and revoked the problematic update within hours, but the damage was already widespread. Falcon Sensor is deployed on over 100 million endpoints globally, primarily in Fortune 500 companies and critical infrastructure.
Immediate Fallout: Airlines Grounded, Chaos Ensues
The outage hit hardest in transportation. Delta Air Lines, one of the largest U.S. carriers, canceled over 1,000 flights by July 20 and reports thousands more disruptions into this week. United Airlines and American Airlines also faced delays, with crews and passengers stranded worldwide.
At airports from London's Heathrow to New York's JFK, digital check-in kiosks, baggage systems, and flight scheduling software failed. Passengers shared videos of massive lines and manual ticketing processes reminiscent of pre-digital eras.
Healthcare providers were equally vulnerable. The UK's National Health Service (NHS) reported outages at GP practices, forcing reliance on paper records. In the U.S., hospitals like those in Kansas City diverted ambulances due to failed electronic health record systems.
Financial services took a hit too. Trading platforms, payment processors, and banks experienced downtime. While core banking functions largely held, customer-facing apps and ATMs stuttered, leading to transaction delays.
Retail giants such as Starbucks saw point-of-sale systems crash, resulting in cash-only operations. Even government agencies, including parts of the U.S. Department of Homeland Security, reported impacts.
Technical Deep Dive: Why It Happened
Experts dissecting the incident point to the Falcon Sensor's deep integration with the Windows kernel. The sensor runs at the highest privilege level (Ring 0) to monitor for threats in real-time, making it powerful but risky.
The buggy channel file, part of CrowdStrike's threat intelligence feed, failed a bounds check during parsing. This caused an out-of-bounds memory read, triggering the kernel panic. macOS and Linux users were unaffected, as the update was Windows-specific.
Microsoft, whose Azure cloud and Windows ecosystem bore the brunt, confirmed no vulnerability in their OS was exploited. "This is not a security incident or cyberattack," Microsoft stated, emphasizing it's a third-party driver issue.
Recovery is manual and painstaking. Affected machines require booting into Safe Mode or Windows Recovery Environment (WinRE), deleting the faulty file from C:\Windows\System32\drivers\CrowdStrike\C-00000291.sys, and rebooting. Automated tools are emerging, but enterprises with thousands of devices face days of labor.
CrowdStrike and Microsoft's Response
CrowdStrike CEO George Kurtz issued a public apology on July 19: "We know this is frustrating... This is not a cyberattack. It is a defect found in one of our channel files." The company activated its incident response teams and published remediation guides.
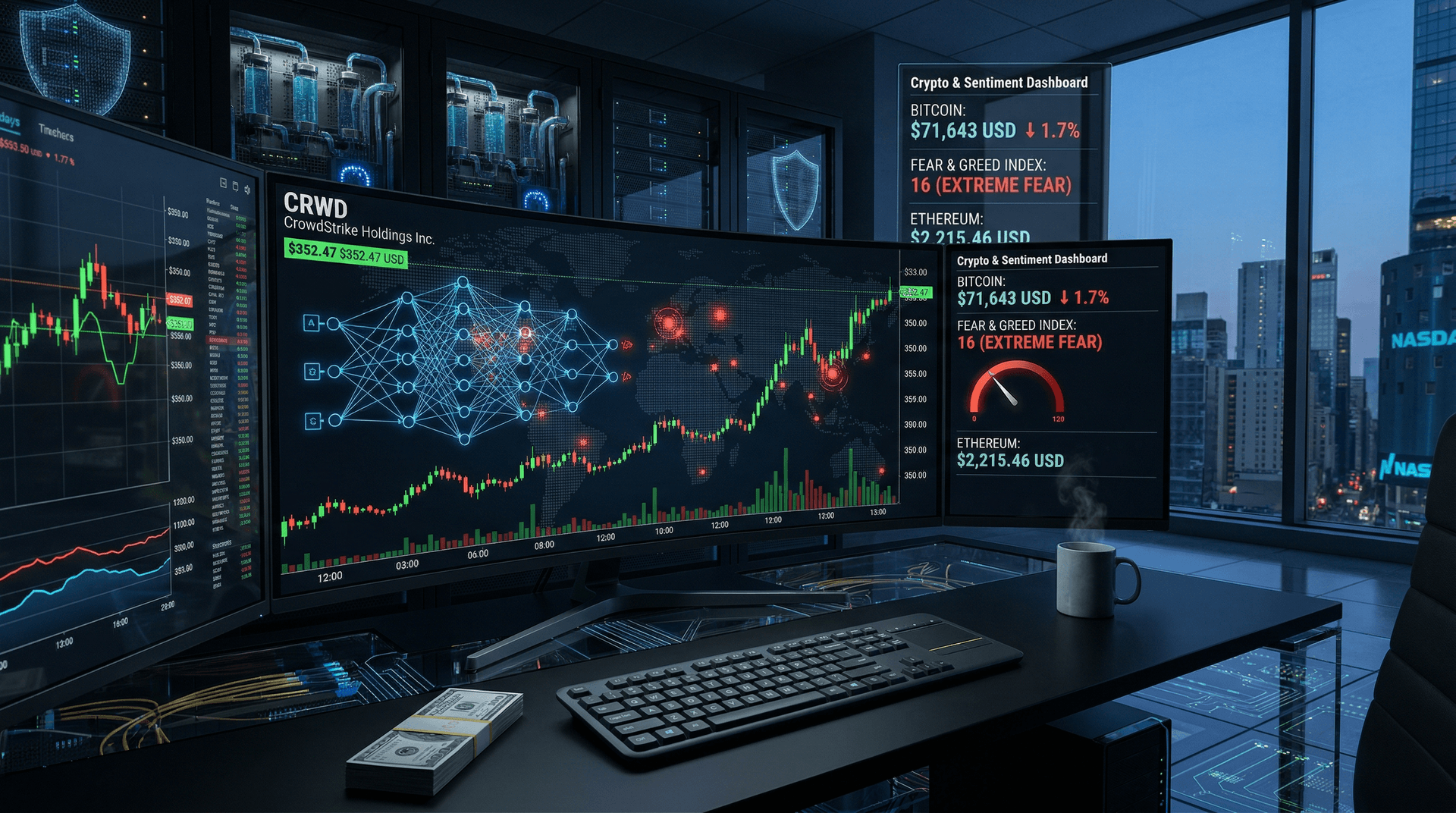
By July 23, CrowdStrike reports over 50% of sensors back online, but full recovery lags. They've halted new content deployments and implemented rigorous validation.
Microsoft jumped in with a dedicated support portal, recovery images, and partnerships with OEMs like Dell and HP. CEO Satya Nadella tweeted: "We are working around the clock with CrowdStrike and customers."
Broader Implications for Cybersecurity
This event underscores the double-edged sword of aggressive cybersecurity tools. EDR platforms like Falcon provide vital protection but introduce single points of failure. A vendor's mistake can cascade globally, far worse than many ransomware attacks.
Analysts draw parallels to the 2020 SolarWinds supply chain compromise, but note this was accidental. "It's a wake-up call for diversification," says Gartner analyst Gregg LeBlanc. "Enterprises must test updates in staging environments and maintain offline recovery options."
Regulators are watching. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued alerts urging manual fixes and binded the incident to its Known Exploited Vulnerabilities catalog indirectly through advisory.
In Europe, the NIS2 Directive may prompt scrutiny of critical third-party providers. Questions arise: Should kernel-level drivers undergo mandatory third-party audits?
As of July 23: Slow Recovery, Lingering Disruptions
Today, Delta resumes limited flights but warns of irregular schedules through the weekend. NHS services normalize, but backlogs persist. CrowdStrike's status page shows progress, yet some sectors report 20-30% downtime.
Economic toll mounts: Estimates peg losses at $1-5 billion daily during peak disruption, per Paramount. Insurance claims for business interruption could follow.
Stock impacts are telling: CrowdStrike shares dropped 11% on July 19 but recover slightly. Microsoft dipped marginally.
Lessons for the Future
1. Update Hygiene: Stagger rollouts, canary deployments, and rollback mechanisms are non-negotiable. 2. Vendor Risk Management: Assess third-party update frequency and kernel access. 3. Resilience Engineering: Air-gapped backups, multi-vendor EDR, and bootable recovery media. 4. Incident Preparedness: Tabletop exercises now include "friendly fire" scenarios.
Cybersecurity's promise of vigilance ironically exposed its pitfalls. As systems interconnect further, one faulty bit can halt the world. CrowdStrike vows transparency via a post-incident review, but trust rebuilds slowly.
This outage reminds us: In the digital age, security isn't just defending against foes—it's safeguarding against ourselves.
Word count: 1,028