In a blog post published on January 19, 2024, Microsoft confirmed what many in the cybersecurity community feared: a brazen intrusion by Russian state-sponsored hackers into its own corporate systems. The attackers, tracked as Midnight Blizzard (also known as Nobelium), gained unauthorized access to a small number of corporate email accounts belonging to senior leadership and employees in cybersecurity and legal divisions. This disclosure comes at a time when geopolitical tensions are fueling an uptick in cyber operations attributed to nation-states.
The Breach Unfolds
The intrusion began in late November 2023, according to Microsoft's timeline. Hackers exploited a stolen legacy test tenant account credential—likely harvested from a prior breach elsewhere. Using this foothold, they authenticated via the Microsoft Entra app in the corporate environment on January 17, 2024. From there, they viewed emails and attachments in accounts of a leadership team member and subsequently targeted the security and legal teams.
Microsoft emphasized that the attack was password-based, not involving exploitation of product vulnerabilities in Microsoft services. "No customer environments, production systems, or production source code were accessed," the company stated. However, the hackers did screenshot and export some email content, prompting Microsoft to notify affected employees and federal law enforcement.
This isn't Midnight Blizzard's first rodeo with Microsoft. The group, believed to be affiliated with Russia's SVR foreign intelligence service, orchestrated the infamous 2020 SolarWinds supply chain attack, compromising nine U.S. federal agencies and over 100 private organizations. That operation infected software updates, allowing backdoor access for espionage.
Microsoft's Defensive Measures
Upon detection—facilitated by a "validation process unrelated to this incident," Microsoft said—the company swiftly revoked the attackers' access. It locked down affected accounts, implemented stricter conditional access policies, and launched a full forensic investigation with external experts. The firm is also reaching out to affected individuals and plans to share indicators of compromise (IOCs) with the cybersecurity community.
"We are aggressively hunting for additional activity by Midnight Blizzard across our environments and have taken additional measures to protect our systems," Microsoft Vice President of Security Operations, Charlie Bell, wrote in the blog. The company committed to transparency, vowing to update the community as the investigation progresses.
Cybersecurity experts praise the disclosure's candor but question why it took two months to detect and publicize. "Microsoft's handling shows maturity, but the fact that legacy credentials lingered highlights a common blind spot," said John Hultquist, VP of Intelligence Analysis at Mandiant, in an interview with CSN News.
Broader Implications for Cybersecurity
This breach arrives amid a surge in state-sponsored cyber activity. Just days earlier, on January 17, AT&T disclosed a massive data leak affecting 73 million customer accounts, traced to a third-party cloud provider. Meanwhile, U.S. agencies have warned of Chinese group Volt Typhoon pre-positioning in critical infrastructure for potential disruption.
Midnight Blizzard's tactics—credential theft followed by lateral movement—mirror those in recent campaigns. The group has targeted government entities, think tanks, and tech firms, often for intelligence on Ukraine and U.S. policy. With the 2024 U.S. presidential election looming, fears of election interference via cyber means are heightened.
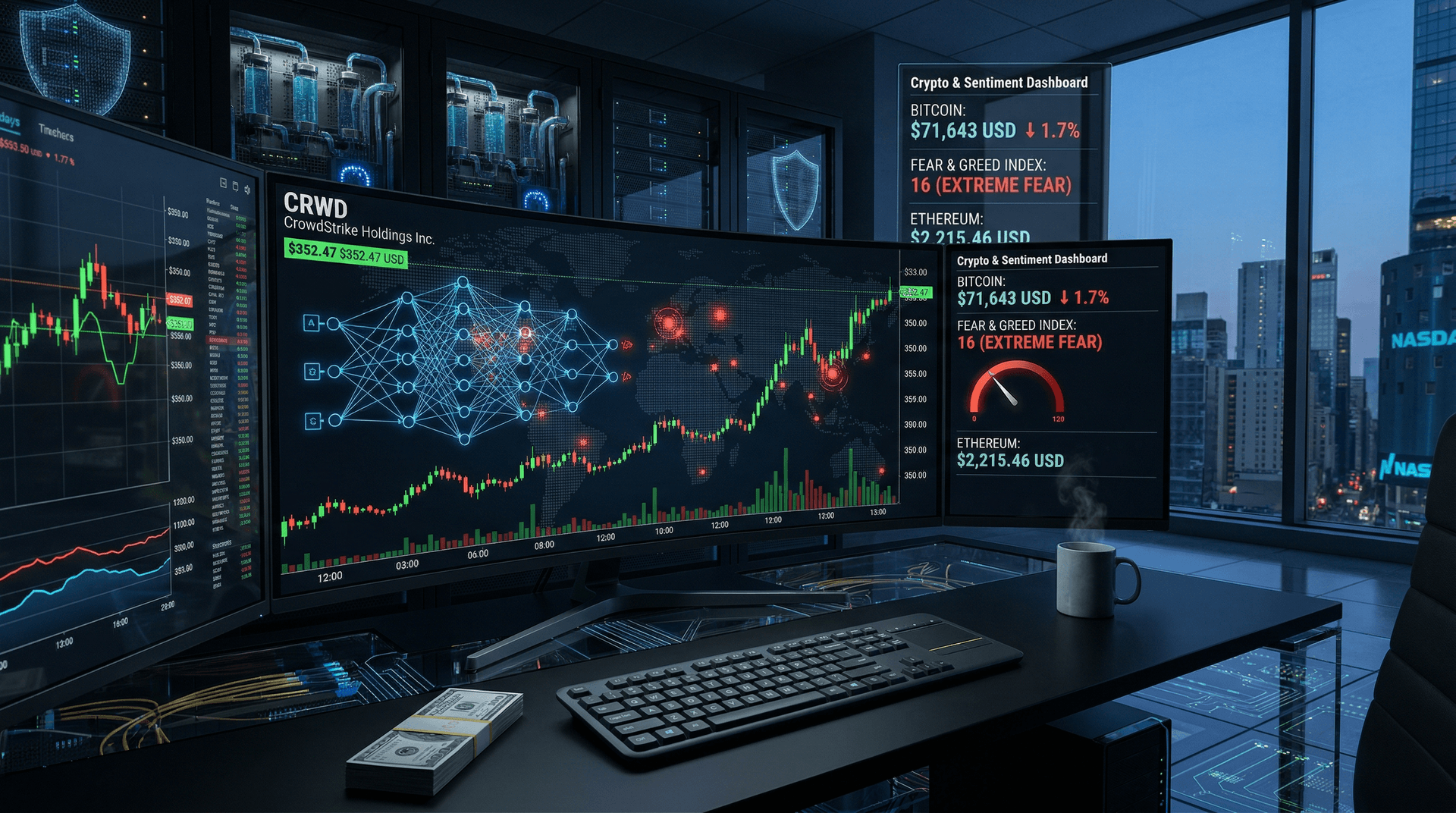
"State actors like Russia are probing for weaknesses everywhere, including in their adversaries' defenders," noted Dmitri Alperovitch, co-founder of CrowdStrike. "Microsoft's breach is a reminder that no one is immune; vigilance must extend to corporate crowns jewels."
The incident also spotlights passwordless authentication's urgency. Microsoft has pushed Entra ID and passkeys, yet legacy systems persist. Industry-wide, multi-factor authentication (MFA) adoption lags, with phishing-resistant methods even scarcer.
Historical Context: Midnight Blizzard's Playbook
Tracking back to 2015, Midnight Blizzard (formerly Cozy Bear or APT29) has refined its espionage toolkit. Post-SolarWinds, the group shifted to spear-phishing and password spraying. In 2021, it hit HAFNIUM exploiting Exchange Server flaws, affecting thousands.
U.S. officials attribute over 250 intrusions to the group since 2020. Sanctions followed, yet operations continue unabated. Microsoft's breach suggests hackers may seek insights into U.S. cyber defenses or Ukraine aid strategies.
Industry Reactions and Recommendations
Peers like Google and Amazon have faced similar scrutiny. Last year, Okta disclosed a breach via a third-party support system. The consensus: Assume breach and hunt proactively.
"Organizations should prioritize identity hygiene: rotate credentials, enforce MFA everywhere, and monitor for anomalous Entra logins," advised Krebs on Security's Brian Krebs.
Regulators are circling. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) urged immediate patching and logging review. EU's NIS2 directive looms, mandating breach reports within 24 hours.
Looking Ahead: A Wake-Up Call
Microsoft's candor sets a positive precedent, contrasting opaque responses from firms like MOVEit vendors post-Clop ransomware. As hybrid work blurs lines, corporate networks become prime targets.
For enterprises, lessons abound: Audit legacy accounts, segment environments, and invest in threat hunting. For policymakers, it's a push for public-private cyber defense pacts.
This breach won't be the last. As Russia grinds on in Ukraine, expect more digital salvos. Microsoft's fortress, though cracked, held; the real test is fortifying the ecosystem.
CSN News will monitor developments. Stay tuned for updates.
(Word count: 912)