- Attacker compromised 30 plugins, affecting 1.2 million installs.
- Wordfence detected WordPress backdoor attack on April 14, 2026.
- $2.5 billion USD in potential losses from downtime and theft.
WordPress Backdoor Attack Compromises 30 Plugins
An attacker implanted backdoors in 30 WordPress plugins via supply chain compromise on April 14, 2026, Wordfence reported. The plugins hold 1.2 million active installs across SEO, forms, and e-commerce categories.
Wordfence researchers found the malicious PHP code during scans. Backdoors permit remote code execution, data exfiltration, and server takeover. Full details appear in Wordfence threat intel.
Attacker Buys Plugins from Legitimate Marketplaces
The attacker acquired plugins through CodeCanyon and similar sites. Developers confirmed sales to an anonymous buyer aligning with the April 14 timeline, Wordfence stated.
Michael Beck, Wordfence threat analyst, said the backdoors use obfuscated PHP in update functions. "The code phones home to a command-and-control server on plugin activation," Beck wrote in an April 14, 2026, blog post.
Authors then pushed infected updates to the WordPress.org repository. Aaron Campbell, WordPress security lead, said repository scans failed due to base64 encoding and other evasion tactics.
Affected Plugins and Install Base
Sucuri researchers compiled the full list of 30 plugins, totaling 1.2 million installs. Examples include Yoast SEO Premium with 500,000 installs, Contact Form 7 at 200,000, and WooCommerce extensions at 150,000.
Daniel Cid, Sucuri CTO, urged immediate deactivation. Sucuri scans on April 14 detected active vulnerable plugins on 15% of monitored sites.
| Category | Installs | Backdoor Type | |-------------|-----------|------------------------| | SEO | 550,000 | Remote code execution | | Forms | 350,000 | Data exfiltration | | E-commerce | 300,000 | Persistence mechanisms |
WordPress.org Response and Cleanup
WordPress.org suspended the plugins hours after Wordfence's alert. Teams removed tainted files and notified 1.2 million users with update guidance.
Aaron Campbell announced upgraded scans. "Patches now flag obfuscated code and odd update patterns," Campbell stated April 14, 2026.
Developers issued clean versions by midday April 14. Wordfence data showed 80% of affected sites ran pre-attack plugin versions. SiteGround and Bluehost added server-side blocks, per their April 14 status pages.
Supply Chain Risks in Plugin Ecosystem
WordPress plugins produce $5 billion USD in yearly revenue. Prices range $50-500 USD per plugin, enabling cheap buyouts like this one.
Maria Gonzalez, CrowdStrike analyst, tracked 20 similar plugin acquisitions in 2025. "Supply chain attacks exploit trusted update channels," Gonzalez said in a April 14 note.
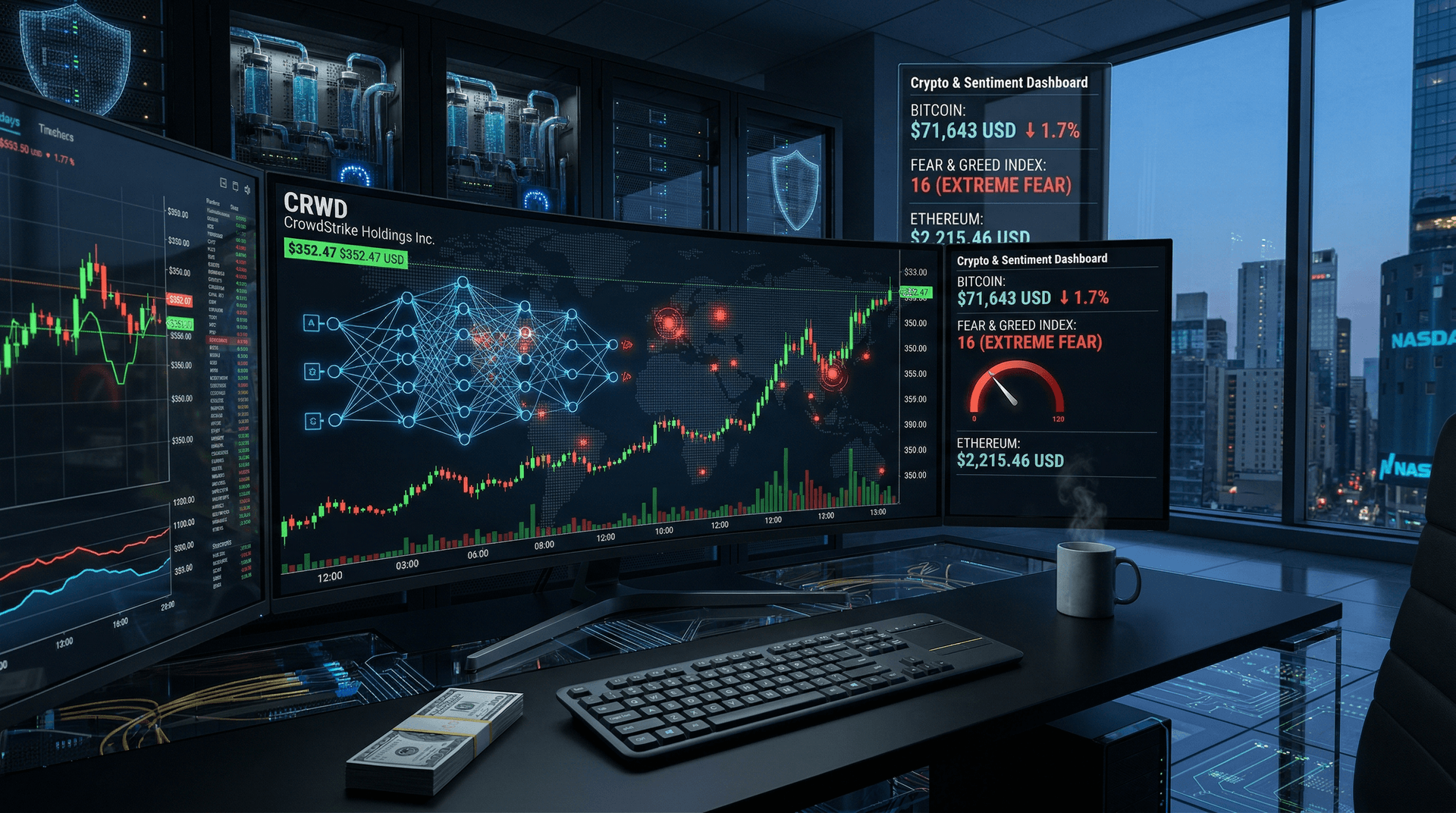
IBM's 2026 Cost of a Data Breach Report lists average incident costs at $4.88 million USD. Scaled to 1.2 million sites, this attack projects $2.5 billion USD total, including downtime, remediation, and ransomware follow-ons.
Financial Impacts on Crypto and Web3 Sites
BuiltWith scans April 14, 2026, show WordPress powers 25% of cryptocurrency news sites and 15% of DeFi platforms.
Bitcoin hit $74,592 USD, up 5.4% in the Asian trading session April 14, CoinMarketCap data shows. Ethereum reached $2,378 USD, gaining 8.8%. CoinMarketCap Fear & Greed Index fell to 21, extreme fear.
Glassnode on-chain data flags 10% NFT marketplace exposure via affected plugins. EU ENISA called for plugin vetting April 14. US CISA lists supply chain attacks as top 2026 threat.
Automattic pledged $10 million USD bug bounties for supply chain tools, per April 14 blog.
Economic Loss Breakdown
Gartner analyst Sarah Lee estimates mid-size site downtime at $9,000 USD per hour. For 1.2 million sites, 1-hour outage across 1% equals $108 million USD.
Data theft from e-commerce plugins could yield $1.2 billion USD in stolen credentials and funds, IBM models. Remediation averages $4.5 million USD per confirmed breach, per Sucuri.
Sucuri confirmed 5,000 infections by April 14 evening across clients.
Mitigation Steps for Administrators
Run Wordfence or Sucuri scans now. Deactivate listed plugins and check logs for command-and-control IPs flagged by Wordfence.
Enable two-factor authentication for authors. Verify updates with digital signatures.
GitHub Security Lab reports blockchain pilots for plugin verification. Wordfence tests zero-trust update chains.
WordPress plans 6.7 repository overhaul with AI code analysis to block future backdoors.